Designing a database schema is one of the most critical tasks in software architecture. A poorly constructed data model can lead to performance bottlenecks, security vulnerabilities, and significant technical debt as the application scales. This guide walks you through the process of creating a robust Entity Relationship Diagram (ERD) specifically tailored for a User Management Service. We will move from initial concept to a production-ready schema, focusing on data integrity, security compliance, and scalability.
📋 Understanding the Scope and Requirements
Before drawing a single line or defining a table, you must understand the functional requirements of the service. A user management system is not merely about storing names and emails; it is about managing identities, permissions, and audit trails. Start by listing the core actors and their interactions.
- Administrators: Require full access to manage other users and system settings.
- End Users: Need to authenticate, update profiles, and access specific features.
- System: Requires automated logging and session management.
Consider the data types and constraints early. Will you support international characters? How do you handle time zones? These decisions influence the field definitions in your diagram. A comprehensive requirements document serves as the blueprint for your ERD, ensuring no critical entity is overlooked during the design phase.
🏗️ Defining Core Entities
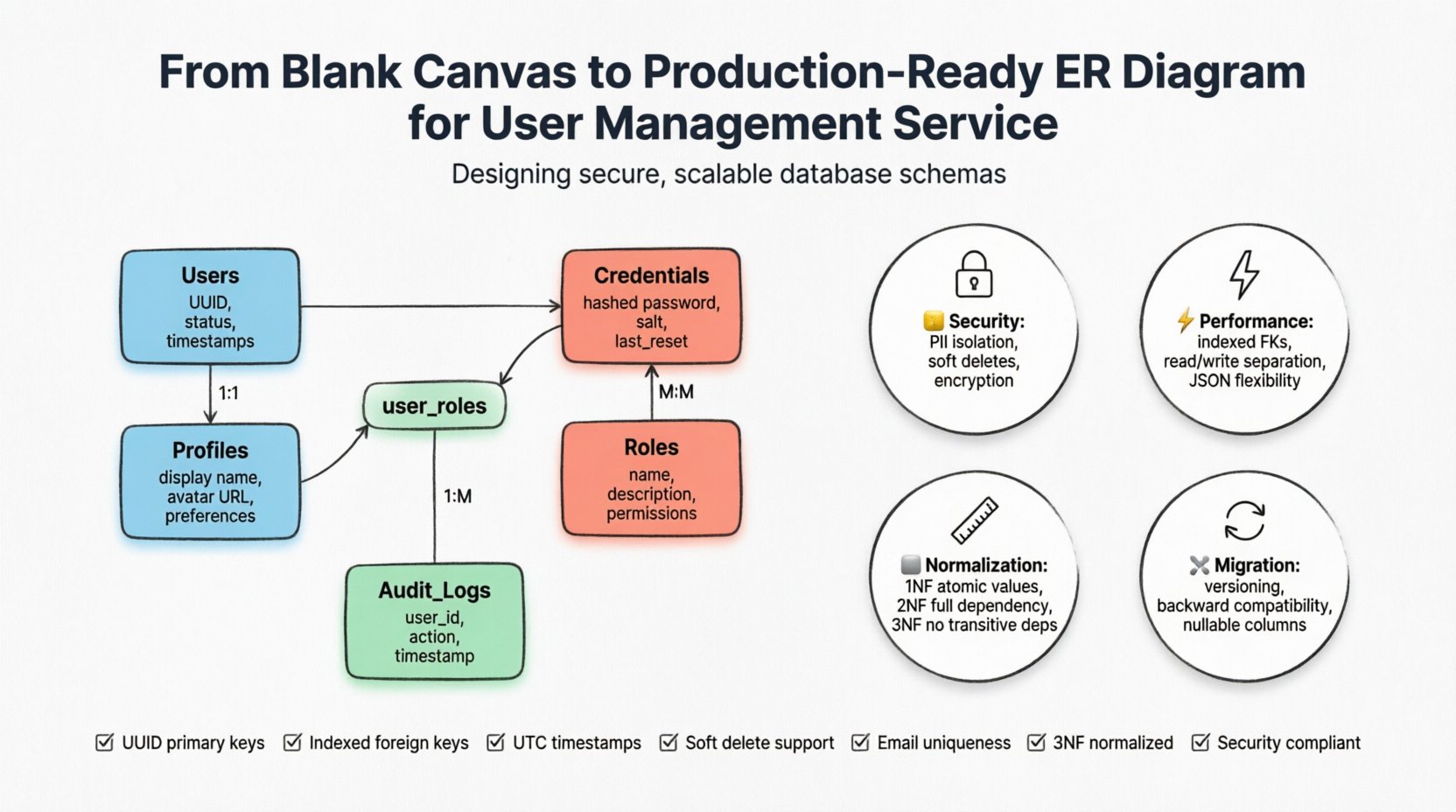
The foundation of any user management system lies in the core entities. These are the tables that will store the persistent data. We will identify five primary entities: Users, Profiles, Credentials, Roles, and Audit Logs.
1. The User Entity
This is the central identity object. It should contain unique identifiers and status flags rather than sensitive data. A well-structured user table includes:
- UUID: A universally unique identifier rather than an auto-incrementing integer. This prevents enumeration attacks and aids in horizontal scaling.
- Status: An enumeration field (e.g., active, suspended, deleted) to control access without deleting records.
- Metadata: Timestamps for creation and last update.
2. The Profile Entity
Storing display names, avatars, and contact information in the main User table can lead to bloat. A Profile entity allows for a one-to-one relationship, keeping the core authentication table lean.
- Display Name: For public-facing visibility.
- Avatar URL: Link to external storage rather than storing binary data.
- Preferences: JSON or a separate table for theme settings and notification preferences.
3. The Credentials Entity
Security is paramount. Authentication details should be separated from user identity data. This separation allows for easier rotation of security protocols without altering the user identity structure.
- Hashed Password: Never store plain text. Use a strong hashing algorithm.
- Salts: Ensure each user has a unique salt value.
- Last Reset Time: Track password changes for security policies.
🔗 Modeling Relationships and Cardinality
Once entities are defined, the relationships between them must be established. Cardinality defines how many instances of one entity relate to another. Misunderstanding these relationships is a common cause of data redundancy.
| Relationship | Type | Reasoning |
|---|---|---|
| User & Profile | One-to-One | Each user has exactly one profile set of details. |
| User & Roles | Many-to-Many | A user can hold multiple roles, and a role can be assigned to many users. |
| User & Audit Logs | One-to-Many | A single user action generates one log entry, but one user generates many logs. |
| Role & Permissions | Many-to-Many | Roles define permissions, but permissions can be shared across roles. |
To implement a Many-to-Many relationship, you must introduce a junction table. For example, between Users and Roles, create a user_roles table. This table contains foreign keys pointing to the primary keys of both the User and Role tables. This structure ensures referential integrity and allows for flexible permission assignments.
📉 Normalization and Data Integrity
A production-ready schema adheres to normalization principles to reduce redundancy. While Third Normal Form (3NF) is the standard goal, understanding the trade-offs is essential.
First Normal Form (1NF)
Ensure every column contains atomic values. Avoid storing multiple email addresses in a single column. Use a separate table for contacts if a user has multiple verified emails.
Second Normal Form (2NF)
Ensure non-key attributes are fully dependent on the primary key. In a composite key scenario, ensure no partial dependencies exist. For user management, using a single UUID as the primary key simplifies this process significantly.
Third Normal Form (3NF)
Ensure no transitive dependencies exist. If a user’s country determines their tax rate, store the country separately from the user table, and link the user to the country. This allows updates to tax rates without modifying every user record.
Normalization is not just about theory; it is about maintaining a single source of truth. When data is duplicated across tables, updates become error-prone. By keeping data atomic, you ensure that consistency is maintained automatically by the database engine.
🔒 Security and Compliance Considerations
A database schema is the first line of defense for user data. Compliance with regulations like GDPR or CCPA requires specific schema design choices.
- PII Isolation: Personally Identifiable Information should be stored in encrypted columns or separate tables with strict access controls.
- Right to be Forgotten: Your schema should support soft deletes or data anonymization. Instead of removing a row, mark it as deleted and replace PII fields with a generic placeholder.
- Audit Trails: Implement an immutable log table. Record who changed what data and when. This is crucial for accountability.
- Encryption at Rest: Design fields that store sensitive data to be compatible with database-level encryption features.
Consider the retention policy for your logs. A table that grows indefinitely can degrade performance. Implement a partitioning strategy for the Audit Log table, archiving older records to cold storage or deleting them based on policy.
⚡ Performance and Scalability Patterns
Designing for production means anticipating load. A schema that works for 100 users may fail at 100,000 users. Indexing strategies are a critical part of the ERD design process.
Indexing Foreign Keys
Always index foreign key columns. If you query users by their role ID, the database needs an index on the foreign key column to avoid a full table scan. This is a common oversight in early designs.
Read vs. Write Separation
While the ERD defines the logical structure, consider physical separation. User authentication data (Credentials) is read-heavy. Profile data is read-heavy. Audit logs are write-heavy. Designing the schema to support sharding or read replicas later is easier if the entity boundaries are clear.
JSON Fields for Flexibility
Modern databases support JSON columns. Use these for attributes that vary significantly between users, such as custom fields or settings. This prevents schema migration for every new feature, though it comes at the cost of query performance.
🛠️ Migration and Lifecycle Management
A production database is never static. It evolves as requirements change. The ERD must accommodate this evolution.
- Versioning: Do not alter tables directly in production. Use migration scripts that create new tables and copy data, then switch references.
- Backward Compatibility: When adding a column, allow it to be nullable initially. This prevents breaking existing application code that does not immediately set the value.
- Constraints: Start with relaxed constraints and tighten them as data stabilizes. Enforcing strict uniqueness too early can halt development.
Consider adding a version column to major tables. This allows you to track schema changes if you implement application-level versioning for data structures.
🚧 Common Pitfalls to Avoid
Even experienced architects make mistakes. Review your diagram against these common issues before deployment.
- Storing Sensitive Data in Logs: Ensure the Audit Log table does not inadvertently capture passwords or credit card numbers. Mask PII in log entries.
- Over-Indexing: Every index slows down write operations. Only index columns used frequently in WHERE clauses or JOINs.
- Ignoring Time Zones: Store all timestamps in UTC. Convert to local time only at the presentation layer. This prevents issues during daylight saving time changes.
- Hardcoded Values: Do not hardcode role names or status values in the application code. Define them as enumerations or lookup tables in the database.
✅ Final Validation Checklist
Before considering the ERD complete, run through this checklist to ensure readiness.
- Are all primary keys UUIDs or auto-increment integers?
- Are all foreign keys indexed?
- Is there a unique constraint on email addresses or usernames?
- Are timestamps stored in UTC?
- Is there a mechanism for soft deletes?
- Is sensitive data separated from identity data?
- Are there indexes for common query patterns?
- Is the schema normalized to at least 3NF?
- Does the design support the required security compliance standards?
A thorough review of these points ensures that the foundation of your user management service is solid. The effort invested in the design phase pays dividends in maintenance, security, and performance over the lifecycle of the application.
📝 Summary of Schema Components
To consolidate the design elements, here is a summary of the key components required for a high-quality user management database.
| Component | Key Fields | Constraint |
|---|---|---|
| Users | id, status, created_at | Primary Key, Unique Status |
| Credentials | user_id, hash, salt, last_reset | Foreign Key, Not Null |
| Roles | id, name, description | Primary Key, Unique Name |
| User_Roles | user_id, role_id | Composite Primary Key |
| Audit_Logs | id, user_id, action, timestamp | Foreign Key, Index on User |
By adhering to these guidelines and structural patterns, you establish a reliable system capable of handling complex user interactions securely. The resulting ERD serves as a contract between the data and the application, ensuring stability as your service grows.